A cyberattack could wreak destruction comparable to a nuclear weapon
- Written by Jeremy Straub, Assistant Professor of Computer Science, North Dakota State University
People around the world may be worried about nuclear tensions rising, but I think they’re missing the fact that a major cyberattack could be just as damaging – and hackers are already laying the groundwork.
With the U.S. and Russia[1] pulling out of a key nuclear weapons pact[2] – and beginning to develop new nuclear weapons[3] – plus Iran tensions[4] and North Korea again test-launching missiles[5], the global threat to civilization[6] is high. Some fear a new nuclear arms race[7].
That threat is serious – but another could be as serious, and is less visible to the public. So far, most of the well-known hacking incidents[8], even those with foreign government backing[9], have done little more than steal data[10]. Unfortunately, there are signs that hackers have placed malicious software[11] inside U.S. power and water systems, where it’s lying in wait[12], ready to be triggered. The U.S. military has also reportedly penetrated the computers that control Russian electrical systems[13].
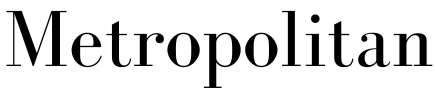
 Students and their teacher practice ‘duck and cover’ during the Cold War.
AP Photo/Dan Grossi[14]
Students and their teacher practice ‘duck and cover’ during the Cold War.
AP Photo/Dan Grossi[14]
Many intrusions already
As someone who studies cybersecurity[15] and information warfare[16], I’m concerned that a cyberattack with widespread impact, an intrusion in one area that spreads to others[17] or a combination[18] of lots of smaller attacks, could cause significant damage, including mass injury and death rivaling the death toll of a nuclear weapon.
Unlike a nuclear weapon, which would vaporize people within 100 feet and kill almost everyone within a half-mile[19], the death toll from most cyberattacks would be slower. People might die from a lack of food, power or gas for heat[20] or from car crashes resulting from a corrupted traffic light system[21]. This could happen over a wide area, resulting in mass injury and even deaths.
This might sound alarmist, but look at what has been happening in recent years, in the U.S. and around the world.
In early 2016, hackers took control of a U.S. treatment plant[22] for drinking water, and changed the chemical mixture[23] used to purify the water. If changes had been made – and gone unnoticed – this could have led to poisonings, an unusable water supply and a lack of water.
In 2016 and 2017, hackers shut down major sections[24] of the power grid in Ukraine[25]. This attack was milder than it could have been, as no equipment was destroyed during it[26], despite the ability to do so. Officials think it was designed to send a message[27]. In 2018, unknown cybercriminals gained access throughout the United Kingdom’s electricity system[28]; in 2019 a similar incursion may have penetrated the U.S. grid[29].
In August 2017, a Saudi Arabian petrochemical plant was hit by hackers who tried to blow up equipment[30] by taking control of the same types of electronics used in industrial facilities of all kinds throughout the world. Just a few months later, hackers shut down monitoring systems for oil and gas pipelines[31] across the U.S. This primarily caused logistical problems – but it showed how an insecure contractor’s systems could potentially cause problems for primary ones.
The FBI has even warned that hackers are targeting nuclear facilities[32]. A compromised nuclear facility could result in the discharge of radioactive material[33], chemicals or even possibly a reactor meltdown. A cyberattack could cause an event similar to the incident in Chernobyl[34]. That explosion, caused by inadvertent error, resulted in[35] 50 deaths and evacuation of 120,000 and has left parts of the region uninhabitable for thousands of years into the future.
 A test of a North Korean missile.
KRT via AP Video[36]
A test of a North Korean missile.
KRT via AP Video[36]
Mutual assured destruction
My concern is not intended to downplay the devastating and immediate effects of a nuclear attack. Rather, it’s to point out that some of the international protections against nuclear conflicts don’t exist for cyberattacks. For instance, the idea of “mutual assured destruction[37]” suggests that no country should launch a nuclear weapon at another nuclear-armed nation: The launch would likely be detected, and the target nation would launch its own weapons in response, destroying both nations.
Cyberattackers have fewer inhibitions[38]. For one thing, it’s much easier to disguise the source of a digital incursion than it is to hide where a missile blasted off from. Further, cyberwarfare can start small, targeting even a single phone or laptop[39]. Larger attacks might target businesses[40], such as banks[41] or hotels[42], or a government agency[43]. But those aren’t enough to escalate a conflict to the nuclear scale.
Nuclear grade cyberattacks
There are three basic scenarios for how a nuclear grade cyberattack might develop. It could start modestly, with one country’s intelligence service stealing, deleting or compromising another nation’s military data. Successive rounds of retaliation could expand the scope of the attacks and the severity of the damage to civilian life.
In another situation, a nation or a terrorist organization could unleash a massively destructive cyberattack – targeting several electricity utilities, water treatment facilities or industrial plants at once, or in combination with each other to compound the damage.
Perhaps the most concerning possibility, though, is that it might happen by mistake. On several occasions, human and mechanical errors very nearly destroyed the world[44] during the Cold War; something analogous could happen in the software and hardware of the digital realm.
 A cyberattack wouldn’t be launched from a nuclear operator’s console, like the one shown here from the decommissioned Oscar Zero site, but rather through cyberspace. A human might not even be required.
Jeremy Straub
A cyberattack wouldn’t be launched from a nuclear operator’s console, like the one shown here from the decommissioned Oscar Zero site, but rather through cyberspace. A human might not even be required.
Jeremy Straub
Defending against disaster
Just as there is no way to completely protect against a nuclear attack, there are only ways to make devastating cyberattacks less likely.
The first is that governments, businesses and regular people need to secure their systems to prevent outside intruders from finding their way in, and then exploiting their connections and access to dive deeper.
Critical systems, like those at public utilities, transportation companies and firms that use hazardous chemicals, need to be much more secure. One analysis found that only about one-fifth of companies that use computers to control industrial machinery[45] in the U.S. even monitor their equipment to detect potential attacks – and that in 40% of the attacks they did catch, the intruder had been accessing the system for more than a year[46]. Another survey found that nearly three-quarters of energy companies[47] had experienced some sort of network intrusion in the previous year.
 Industrial control rooms like this often contain vulnerable computer systems.
nostal6ie/Shutterstock.com[48]
Industrial control rooms like this often contain vulnerable computer systems.
nostal6ie/Shutterstock.com[48]
But all those systems can’t be protected without skilled cybersecurity staffs to handle the work. At present, nearly a quarter[49] of all cybersecurity jobs in the U.S. are vacant, with more positions opening up[50] than there are people to fill them. One recruiter has expressed concern that even some of the jobs that are filled are held by people who aren’t qualified[51] to do them. The solution is more training and education, to teach people the skills they need to do cybersecurity work, and to keep existing workers up to date on the latest threats and defense strategies.
If the world is to hold off major cyberattacks[52] – including some with the potential to be as damaging as a nuclear strike – it will be up to each person, each company, each government agency to work on its own and together to secure the vital systems on which people’s lives depend.
References
- ^ U.S. and Russia (www.nytimes.com)
- ^ key nuclear weapons pact (www.cbsnews.com)
- ^ beginning to develop new nuclear weapons (allthingsnuclear.org)
- ^ Iran tensions (www.usnews.com)
- ^ again test-launching missiles (theconversation.com)
- ^ global threat to civilization (thebulletin.org)
- ^ new nuclear arms race (www.pbs.org)
- ^ most of the well-known hacking incidents (www.nytimes.com)
- ^ foreign government backing (www.cnbc.com)
- ^ steal data (www.forbes.com)
- ^ hackers have placed malicious software (arstechnica.com)
- ^ lying in wait (www.technologyreview.com)
- ^ computers that control Russian electrical systems (www.nytimes.com)
- ^ AP Photo/Dan Grossi (www.apimages.com)
- ^ cybersecurity (dl.acm.org)
- ^ information warfare (theconversation.com)
- ^ that spreads to others (i-hls.com)
- ^ combination (tedkoppellightsout.com)
- ^ which would vaporize people within 100 feet and kill almost everyone within a half-mile (nymag.com)
- ^ lack of food, power or gas for heat (theconversation.com)
- ^ corrupted traffic light system (theconversation.com)
- ^ took control of a U.S. treatment plant (www.theregister.co.uk)
- ^ changed the chemical mixture (www.securityweek.com)
- ^ major sections (www.wired.com)
- ^ power grid in Ukraine (www.wired.com)
- ^ equipment was destroyed during it (en.wikipedia.org)
- ^ designed to send a message (www.wired.com)
- ^ throughout the United Kingdom’s electricity system (unearthed.greenpeace.org)
- ^ penetrated the U.S. grid (www.eenews.net)
- ^ hackers who tried to blow up equipment (www.nytimes.com)
- ^ monitoring systems for oil and gas pipelines (threatpost.com)
- ^ hackers are targeting nuclear facilities (www.nytimes.com)
- ^ discharge of radioactive material (www.nytimes.com)
- ^ incident in Chernobyl (www.theatlantic.com)
- ^ resulted in (www.theatlantic.com)
- ^ KRT via AP Video (www.apimages.com)
- ^ mutual assured destruction (ssi.armywarcollege.edu)
- ^ fewer inhibitions (twitter.com)
- ^ phone or laptop (theconversation.com)
- ^ businesses (www.nytimes.com)
- ^ banks (www.cnn.com)
- ^ hotels (www.forbes.com)
- ^ government agency (gizmodo.com)
- ^ nearly destroyed the world (taskandpurpose.com)
- ^ only about one-fifth of companies that use computers to control industrial machinery (www.darkreading.com)
- ^ accessing the system for more than a year (www.darkreading.com)
- ^ nearly three-quarters of energy companies (www.automation.com)
- ^ nostal6ie/Shutterstock.com (www.shutterstock.com)
- ^ nearly a quarter (www.cyberseek.org)
- ^ more positions opening up (www.csoonline.com)
- ^ held by people who aren’t qualified (www.csoonline.com)
- ^ hold off major cyberattacks (www.vice.com)
Authors: Jeremy Straub, Assistant Professor of Computer Science, North Dakota State University